Directory Browsing Gives Hackers Information About Your Site
Hackers are always looking for sources of information that will lead them to find vulnerabilities in websites. Find out about directory browsing and what you can do to protect your WordPress website from hackers.
Let’s call it ‘Directory Browsing’. What is it?
Common WordPress vulnerabilities can be found in outdated plugins, themes and weaker login credentials. The lesser-known vulnerability among WordPress website owners is the ‘Directory Browsing Vulnerability.’ Some call it ‘Directory Listing Vulnerability.’ This vulnerability is different to the others mentioned earlier, as it is a known vulnerability within the web hosting itself when index.php or index.html files are missing within the directories located on the server. The result is an exposed, vulnerable and easily accessible directory structure, as are the files, folders and contents within.
- Directory browsing is made easy due to web hosting servers being configured to display directories, as well as being able to display web site pages.
- Directory browsing can be explained as ‘anyone being able to gain access to a website using a web browser, rather than accessing it from a web page. Primarily this happens when an index.html file or index.php can’t be found in the directory.
- Hackers may use this practice to see a list of files and folders and the contents within them.
What’s the immediate danger? What are the risks?
- Privacy, security and information disclosure are the first two that come to mind. Most of us have the all-important privacy policy on our website. This issue is a direct breach of the said policy and its governing laws. Hackers want to exploit these vulnerabilities.
- Within the wp-includes directories and files stored within the Cpanel > File Manager is a lot of data entrusted to you buy those who even use your contact form, as well as having direct access to a ton of information about the way your website is constructed.
- The directory browsing vulnerability in WordPress isn’t good for web designers as their creations can be copied. The designer’s reputation is at stake by creating websites with this vulnerability.
What will the hackers be able to see and what will they have access to?
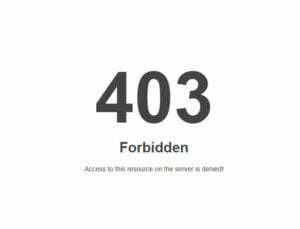
The Index of the folders in wp-includes can be accessed and seen and accessed by hackers if a security measure isn’t put in place. See the snapshot below of what they can see and what you will be able to see when you run the test.
TEST: Check Your Site For The Vulnerability
- To find out if your site has this vulnerability, go to the address bar on your web browser.
- Type in your web address with a /wp-includes as an extension then enter.
- If you can see a directory listing, your directory browsing Is enabled.
If your site is secure you will see a 403 Forbidden message like the one below:
Disabling Directory Browsing in cPanel (one of many methods)
If you don’t want people to be able to browse your directories, you can easily disable directory browsing via cPanel.
- Log Into the Cpanel
- Scroll down to the Advanced header and find Indexes.
- You will see a bunch of folders.
- Click Edit next to the folder you aim to disable browsing on.
- Select No Indexing for each folder and Save.
The directory browsing feature will now be disabled on the selected directory.
Run the test again to make sure your WordPress website is now safe. Run through the settings again for each file or folder until you no longer see a list of files You might need to repeat this action for the files/folders listed if you can to see them listed as above after testing.
The measure above is not the only method of hardening your WordPress website against vulnerabilities. For that, you will need to install a firewall, create strong user names and passwords, install a security plugin with a firewall to scan for malware and keep potential hackers out.
Further instructions can be found on this video and on the WP Beginner website which is a fantastic resource for WordPress users and freelancers.
If you have any questions about this WordPress vulnerability or if you need help with securing your WordPress website, get in touch.
Sandra Ciminelli.
WordPress Web Design, Development and Help
More details and other methods of fixing the vulnerability can be found on BlogVault.net.